A rash of users with “There is no connected camera.” problems with their Mac iSight Cameras has prompted a few calls on the subject. The problem manifests as a blank screen with a crossed out camera in iPhoto, with the text “There is no connected camera”. It does not appear to be limited to any particular type of Mac, and has been seen on a brand new 2017, top of the range MacBook Pro within a few weeks of purchase.
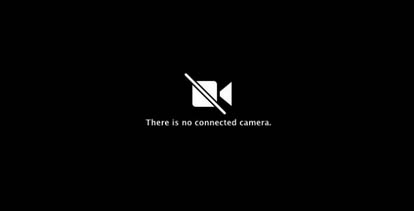
The error message “There is no connected camera.” comes up when the iMac, MacBook, MacBook Pro or MacBook Air detects an issue with the camera’s connection. The problem appears to be with VDCAssistant, which is the process or daemon that is responsible for the built in iSight camera. Killing this process often fixes issues with the built in web-cam.
To Diagnose ‘There is no connected camera.’
First check If The OS recognises that the camera is installed by doing the following:
- Alt + Click on Apple (Top Left)
- Then Alt + Click System Information
- Under Hardware in the Left Column, click Camera
If no camera appears, then there may be a hardware problem, such as a lose ribbon connection on a laptop, so it is a trip to the Genius Bar or your local Tech Support.
How To Kill the VDCAssistant Process
If the camera is recognised then it is possible that the VDCAssistant process has stalled. To kill the VDCAssistant and any associated processes, close all applications1 that use the camera such as Photo Booth, Face Time or Skype. Then carry out the following steps:
- Open the Terminal application: Click on the Spotlight search and enter Terminal, and then select Terminal – Utilities.
- Enter sudo killall VDCAssistant in the Terminal window and hit Return.
- If the Password prompt appears, enter your password, followed by Return.
Open Photo Booth and see if the camera is working. The green camera light should be on
Still ‘There is no connected camera.’?
If the camera has now been restored, then the process has been killed and then successfully restarted. You can also kill the process by restarting the machine, although that is not always convenient. If you still get the error message “There is no connected camera.”, then the quick fix did not work, and there is a more challenging problem to deal with. In this case it is off to the Apple Genius Bar2 or your local Tech Support. If this did not help, please Contact Us to let us know.
Notes
1. Although not recommended, it is possible to do this with the application(s) running, as the VDCAssistant process will restart automatically.
2. Other support channels are available to help with the error “There is no connected camera.”